Kubernetes has become the backbone of modern application delivery, but many teams still treat security as a final checklist item. That approach creates risk. The Certified Kubernetes Security Specialist (CKS) path is valuable because it helps professionals build security into Kubernetes environments from the start—during setup, deployment, and runtime.This master guide is written for working engineers, software professionals, and managers (India + global) who want a practical and career-focused understanding of CKS. The goal is to help you understand what CKS is, who should pursue it, how to prepare, what skills it builds, and how it connects to bigger career tracks like DevOps, DevSecOps, SRE, AIOps/MLOps, DataOps, and FinOps. The DevOpsSchool CKS page presents the course as a Kubernetes security training path with topics such as cluster setup, hardening, system hardening, supply chain security, and runtime security, and it lists a course duration of 10–15 hours in the training format shown there.
Why the Certified Kubernetes Security Specialist Matters
Many engineering teams can deploy to Kubernetes, but fewer teams can secure Kubernetes well. Real-world problems usually come from common gaps:
- Over-permissioned access
- Weak secrets handling
- Unsafe default settings
- Poor workload isolation
- Low visibility at runtime
CKS matters because it trains people to think beyond “deployment success” and focus on secure operations. The referenced CKS page describes the certification as important for Kubernetes security expertise, industry recognition, practical skills, and the ability to secure applications during build, deployment, and runtime.
For companies, this means fewer avoidable mistakes and stronger platform governance. For professionals, it means better credibility for cloud-native security work.
What Is Certified Kubernetes Security Specialist (CKS)?
The Certified Kubernetes Security Specialist (CKS) is a Kubernetes security-focused certification path for professionals responsible for securing Kubernetes environments. The DevOpsSchool CKS page states that it is aimed at professionals such as Kubernetes administrators, cloud administrators, and security specialists, and it highlights security topics across the Kubernetes lifecycle.
What it is
CKS is a practical, security-centered Kubernetes certification path. It focuses on securing cluster components, workloads, software supply chains, and runtime behavior in real environments—not just learning theory.
Who should take it
- Kubernetes Administrators
- DevOps Engineers
- DevSecOps Engineers
- SREs (Site Reliability Engineers)
- Platform Engineers
- Cloud Engineers
- Security Engineers working with containers/Kubernetes
- Software Engineers deploying services on Kubernetes
- Engineering Managers who lead cloud-native teams
Skills you’ll gain
- Kubernetes security fundamentals and secure-by-design thinking
- Cluster hardening and access reduction techniques
- RBAC and least-privilege implementation
- Safer pod/workload configuration practices
- Secret handling and configuration hygiene
- Container image and supply chain risk awareness
- Network policy and service isolation skills
- Monitoring, logging, and runtime security basics
- Security troubleshooting in Kubernetes environments
Real-world projects you should be able to do after it
- Build a Kubernetes cluster hardening checklist for your team
- Restrict Kubernetes API access and tighten RBAC permissions
- Apply namespace and workload-level network segmentation
- Create a secure deployment review process for app teams
- Add image scanning and registry controls to CI/CD pipelines
- Improve Kubernetes secret usage standards and rotation workflow
- Enable audit-log-based monitoring for privileged access
- Design a runtime security response checklist for suspicious behavior
Preparation plan (7–14 days / 30 days / 60 days)
7–14 day plan (for experienced Kubernetes users)
- Refresh Kubernetes auth, RBAC, networking, and pods
- Practice daily hardening tasks in short lab sessions
- Focus on weak topics: network policy, supply chain, runtime security
- Do timed task drills to build speed and confidence
30 day plan (best for working professionals)
- Week 1: Kubernetes security basics, authn/authz, RBAC, service accounts
- Week 2: Cluster hardening, system hardening, workload security
- Week 3: Supply chain security, image controls, CI/CD security basics
- Week 4: Monitoring/logging/runtime security + revision + mock practice
60 day plan (for gradual and deeper preparation)
- Month 1: Kubernetes fundamentals + security concepts + lab habit
- Month 2: Domain-by-domain hands-on practice + timed scenarios + revision
- Create your own notes, checklists, and troubleshooting commands
- Repeat practical tasks until they feel natural
Common mistakes
- Studying theory but avoiding hands-on labs
- Jumping into advanced security before mastering Kubernetes basics
- Memorizing YAML without understanding security purpose
- Ignoring RBAC and network policies until late preparation
- Spending too much time reading and too little time practicing
- Skipping runtime security and monitoring topics
- Not practicing under time pressure
- Treating certification prep as separate from real project work
Best next certification after this
Recommended next certification (broad growth option):
Master in DevOps Engineering (MDE)
The DevOpsSchool MDE page describes the program as covering DevOps, DevSecOps, and SRE principles together, with job-ready skills and broader career positioning.
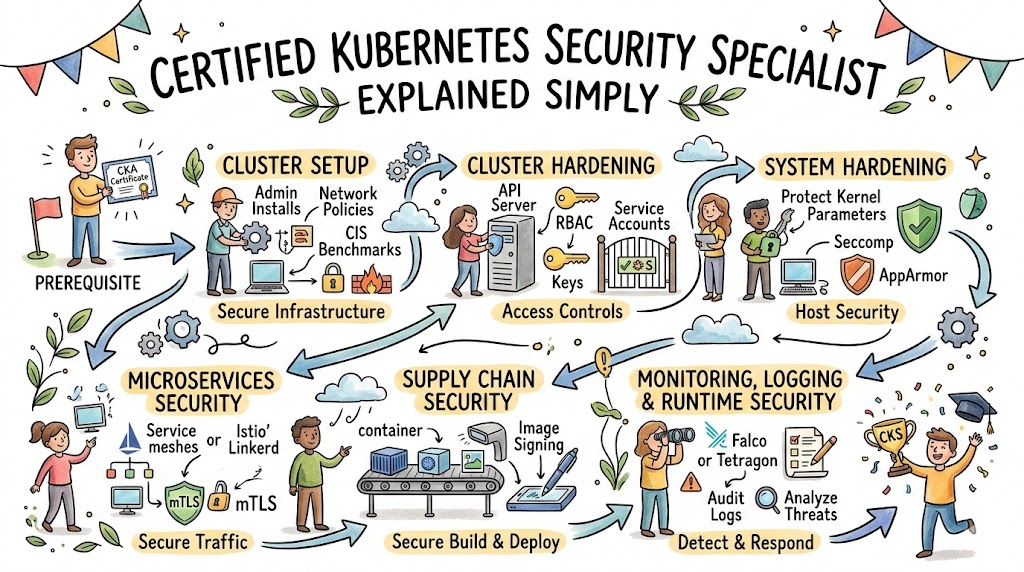
What You Will Learn in CKS
The DevOpsSchool CKS page lists an agenda that includes Cluster Setup, Cluster Hardening, System Hardening, Minimize Microservice Vulnerabilities, Supply Chain Security, and Monitoring/Logging/Runtime Security. These areas map very well to real Kubernetes security responsibilities.
Cluster Setup
This is about creating a safer starting point. The agenda on the CKS page includes tasks such as using network policies, reviewing configurations against CIS benchmark ideas, securing ingress usage, protecting node metadata/endpoints, and verifying platform binaries.
Why this matters in real life: a weak setup creates problems that become expensive later.
Cluster Hardening
The CKS agenda highlights restricting Kubernetes API access, using RBAC to reduce exposure, carefully handling service accounts, and keeping Kubernetes updated.
Why this matters in real life: many production incidents begin with excessive access and poor permission control.
System Hardening
The CKS page’s agenda includes reducing host OS footprint, minimizing IAM roles, limiting external network access, and using kernel hardening tools such as AppArmor and seccomp.
Why this matters in real life: Kubernetes security is not only about manifests; node-level security still matters.
Minimize Microservice Vulnerabilities
The agenda includes secure OS-level domains, Kubernetes secrets management, container runtime sandboxes (such as gVisor/Kata), and pod-to-pod encryption with mTLS.
Why this matters in real life: application teams often need safe defaults and platform guidance.
Supply Chain Security
The CKS agenda lists minimizing base image footprint, registry allowlisting, signing/validating images, static analysis of workloads/Dockerfiles, and image vulnerability scanning.
Why this matters in real life: a secure cluster still becomes risky if unsafe images are deployed.
Monitoring, Logging and Runtime Security
The CKS agenda includes behavioral analytics, threat detection, investigation of bad actors, runtime immutability, and use of audit logs to monitor access.
Why this matters in real life: security controls must continue after deployment.
Certification Table
You requested a table listing every certification with the given fields. Since your prompt centers on CKS and asks for next-step guidance from the MDE page, the table below includes the core certification in this guide and the most relevant next-step certification path.
| Track | Level | Who it’s for | Prerequisites | Skills covered | Recommended order |
|---|---|---|---|---|---|
| Kubernetes Security | Specialist | Kubernetes admins, DevOps/DevSecOps engineers, SREs, Platform/Security engineers | Strong Kubernetes basics, Linux/CLI familiarity, hands-on cluster usage | Cluster setup security, cluster hardening, system hardening, microservice security, supply chain security, monitoring/logging/runtime security | 1 |
| DevOps / DevSecOps / SRE (Broad career path) | Master Program | Engineers, managers, career transitioners, platform/cloud professionals | General IT/software background helpful | DevOps, DevSecOps, and SRE principles, practices, and job-ready skills (as described on MDE page) | 2 |
The MDE page specifically describes the program as a combined DevOps, DevSecOps, and SRE path and includes agenda items such as learning DevOps/DevSecOps/SRE concepts and transition to projects.
How to Approach CKS Preparation With Better Thinking
Many people prepare for certifications by collecting notes, videos, and PDFs. That can help, but CKS rewards a different approach: task-based learning.
Think in “security actions,” not “chapter names”
Instead of saying “Today I will study cluster hardening,” say:
- Today I will reduce API exposure
- Today I will tighten service accounts
- Today I will test network segmentation
- Today I will review image trust controls
This mindset builds skill faster because it connects learning to real work.
Build your own security checklists during prep
While learning, create mini-checklists for:
- New cluster setup review
- Namespace onboarding
- Workload deployment approval
- Image and registry policy review
- Runtime monitoring and incident triage
These checklists become useful in interviews, audits, and your actual job.
Practice communication, not only commands
Managers and senior engineers value people who can explain:
- what the risk is,
- what control was added,
- what trade-off exists,
- and what the impact is.
CKS can become a career accelerant when you combine technical practice with clear decision-making.
Choose Your Path
This section connects CKS to broader career tracks, as requested.
1) DevOps Path
Who this path is for: DevOps Engineers and automation-focused professionals managing CI/CD, infrastructure, and deployments.
CKS helps DevOps professionals move from “I can automate deployments” to “I can automate secure deployments.” This is a major difference in modern teams. Instead of only focusing on speed, you start balancing speed with access control, image safety, and runtime protections.
Suggested progression
- Kubernetes operational basics
- CKS specialization
- Broader DevOps/DevSecOps/SRE growth through MDE
- Senior DevOps / Platform Engineer responsibilities
What becomes stronger
- Secure CI/CD pipeline decisions
- Registry and image governance
- Safer default deployment templates
- Platform-level security standards
2) DevSecOps Path
Who this path is for: Engineers who want security built into delivery pipelines and platform design.
CKS is a strong fit for DevSecOps because Kubernetes is a major runtime platform for modern applications. The CKS agenda includes supply chain security and runtime security, which directly supports DevSecOps thinking.
Suggested progression
- Kubernetes basics + deployment experience
- CKS
- Broaden into DevSecOps process/culture/practices through MDE-aligned learning
- Security automation and policy governance specialization
What becomes stronger
- Secure deployment lifecycle thinking
- Secrets and workload controls
- Runtime visibility and incident readiness
- Security collaboration with developers/platform teams
3) SRE Path
Who this path is for: SREs supporting production systems and platform reliability.
SRE work is about reliability, but security failures often become reliability failures. The MDE page also discusses SRE alongside DevOps and DevSecOps as connected disciplines. CKS helps SREs reduce risk while improving operational stability.
Suggested progression
- Production Kubernetes operations
- CKS
- Expand reliability and org-level practices via MDE path
- Senior SRE / Platform reliability leadership
What becomes stronger
- Secure operational standards
- Incident detection and investigation readiness
- Runtime monitoring perspective
- Risk-aware reliability engineering
4) AIOps/MLOps Path
Who this path is for: Engineers running machine learning and platform workloads on Kubernetes.
Many MLOps platforms depend on Kubernetes for orchestration, serving, and scaling. CKS helps you secure those systems by improving workload isolation, secrets handling, registry hygiene, and runtime controls.
Suggested progression
- Kubernetes for ML platform operations
- CKS
- AIOps/MLOps specialization and tooling depth
- Secure model-serving and platform governance
What becomes stronger
- Secure model deployment workflows
- Access control for shared ML infrastructure
- Safer artifact/image deployment
- Monitoring for unusual runtime behavior in ML services
5) DataOps Path
Who this path is for: Data engineers and data platform teams working with containerized workloads.
Data systems increasingly run on orchestrated platforms. If your pipelines, services, or orchestration components are on Kubernetes, CKS gives you a security layer that improves platform trust and reduces operational risk.
Suggested progression
- Kubernetes data workload operations
- CKS
- DataOps platform and pipeline specialization
- Governance and audit-friendly operations
What becomes stronger
- Secure data platform workload isolation
- Secrets and credentials handling discipline
- Monitoring and logging for operational review
- Safer multi-team platform usage
6) FinOps Path
Who this path is for: FinOps practitioners and engineering teams managing cost and governance in cloud-native platforms.
CKS and FinOps may look like separate worlds, but secure operations often support cost discipline. Poor access control, weak governance, and incidents create waste. Strong Kubernetes security supports safer and more predictable platform operations.
Suggested progression
- Kubernetes platform cost basics
- CKS (for governance/security understanding)
- FinOps specialization and policy collaboration
- Engineering + finance governance leadership
What becomes stronger
- Governance conversations with platform teams
- Cost-risk tradeoff thinking
- Secure shared-cluster practices
- Better policy alignment across teams
Role → Recommended Certifications Mapping
Here is the requested role-based mapping for planning certification progression.
| Role | Recommended certifications | Why this path fits | Next-step focus |
|---|---|---|---|
| DevOps Engineer | CKS → MDE | Adds Kubernetes security depth, then broadens DevOps/DevSecOps/SRE capability | Secure CI/CD, platform ownership, senior delivery roles |
| SRE | CKS → MDE | Improves secure reliability practices and incident readiness | Production hardening, observability, reliability leadership |
| Platform Engineer | CKS → MDE | Strong match for secure cluster/platform design | Internal platform standards, safer defaults, governance |
| Cloud Engineer | CKS → MDE | Builds cloud-native security + broader engineering practices | Secure cloud platform operations and collaboration |
| Security Engineer | CKS → MDE | Deep Kubernetes security + cross-functional delivery understanding | DevSecOps implementation and platform security reviews |
| Data Engineer | CKS (if Kubernetes-based data workloads) → MDE / DataOps specialization | Adds platform security to data infrastructure work | Secure pipeline operations, access boundaries, governance |
| FinOps Practitioner | CKS (optional for Kubernetes-heavy orgs) → FinOps specialization + MDE awareness | Helps connect engineering governance with cost control | Cloud cost policy alignment with platform/security teams |
| Engineering Manager | CKS (awareness + practical understanding) → MDE | Stronger technical oversight and roadmap planning | Team capability mapping, architecture decisions, cross-team leadership |
Next Certifications to Take
You asked for 3 options (same track, cross-track, leadership) and to refer to the MDE page. Below is a practical version built around that request.
1) Same Track Option (Kubernetes Security Depth)
What to do next:
Continue deeper into Kubernetes security implementation after CKS instead of immediately chasing another exam.
Why this is a smart move
- CKS topics are highly practical
- Real project experience compounds certification value
- You can build stronger portfolio examples
Examples of same-track work
- Cluster hardening standards and templates
- Namespace onboarding security checklist
- Runtime monitoring and incident runbooks
- Secure image and registry governance policy
This is best for professionals already working directly on Kubernetes security or platform security.
2) Cross-Track Option (Broader Engineering Growth)
Recommended certification: Master in DevOps Engineering (MDE)
The MDE page positions the program as a broader path covering DevOps, DevSecOps, and SRE principles together, and it includes agenda topics spanning those areas.
Why this is a strong next step after CKS
- CKS gives deep Kubernetes security skill
- MDE helps widen your engineering perspective
- Strong combination for senior roles and architecture discussions
Best for
- DevOps Engineers
- SREs
- Platform Engineers
- Cloud Engineers
- Security Engineers who want broader delivery context
3) Leadership Option (Lead / Manager / Architect Route)
What to do next:
Use CKS + MDE knowledge to take ownership of platform standards, engineering governance, and skill development for teams.
Why this is valuable
Leadership roles need both technical depth and cross-functional understanding. CKS gives security credibility in Kubernetes. MDE helps connect DevOps, DevSecOps, and SRE thinking for team-level planning and execution. The MDE page also emphasizes broader job-ready skills and combined discipline coverage.
Best for
- Engineering Managers
- Lead Engineers
- Platform Leads
- Cloud/DevOps Architects
Top Institutions That Help in Training cum Certifications for CKS
Below is a practical, neutral overview of the institutions/brands you listed. These can be considered by learners comparing ecosystems for training, mentoring, and certification support.
1) DevOpsSchool
DevOpsSchool is directly relevant to this guide because the CKS and MDE pages referenced here are hosted on DevOpsSchool. The CKS page includes course details, target audience, training methodology, agenda, and FAQs, which makes it useful for learners who want a structured training view. It appears to position CKS training as practical and instructor-led, with a focus on Kubernetes security topics across setup, hardening, supply chain, and runtime. For learners who want a larger certification ecosystem and progression options, DevOpsSchool can be a practical choice because it also hosts broader programs like MDE.
2) Cotocus
Cotocus is often considered in conversations around enterprise technology training and consulting support. For learners, it may be useful when they want practical exposure connected to real implementation thinking, not only classroom theory. Professionals who are comparing training providers often look at mentor quality, delivery model, and industry relevance; Cotocus can be evaluated on those factors. It can be especially useful for teams that want combined learning and implementation direction. Learners should always compare course depth and hands-on support before choosing. A structured learning plan matters more than brand name alone.
3) Scmgalaxy
Scmgalaxy has been associated with DevOps and automation learning paths in training discussions for years. It may be a useful starting point for professionals who need stronger fundamentals before moving into specialized tracks like Kubernetes security. Learners preparing for CKS often do better when they already have comfort with tooling, Linux, automation, and platform basics. Scmgalaxy can be considered as part of that foundation-building stage. It is best evaluated based on curriculum quality, lab practice opportunities, and instructor depth. A beginner-friendly path can reduce confusion before advanced certifications.
4) BestDevOps
BestDevOps is another training-focused brand that many learners compare while searching for DevOps and cloud-related programs. It may be helpful for professionals looking for role-based learning journeys and broader technology coverage. For someone preparing for CKS, a provider like this can be useful if it supports prerequisite strengthening in Kubernetes and operations topics. The key point is not only certification preparation, but also whether the training improves job performance and troubleshooting ability. Learners should compare practical assignments, mentoring access, and support quality. Consistent practice matters more than course marketing.
5) devsecopsschool
devsecopsschool is especially relevant for professionals who want a stronger security-first engineering mindset. Since CKS is closely aligned with Kubernetes security and secure operations, a DevSecOps-oriented training ecosystem can be a good next step after CKS or a helpful parallel track. It may support engineers who want to move from Kubernetes security tasks into broader CI/CD security, governance, and policy-focused work. This is valuable for people targeting DevSecOps roles in modern organizations. Learners should look for practical labs, real use cases, and clear implementation guidance. A strong DevSecOps foundation complements CKS well.
6) sreschool
sreschool is useful for professionals who want to improve production reliability, incident thinking, and operational discipline. CKS and SRE knowledge work well together because secure systems are easier to run safely and reliably. SRE-focused training can help CKS learners connect security controls with uptime, error reduction, and incident response workflows. This is a strong combination for platform teams and production operations roles. It can also help managers build more balanced engineering practices across speed, security, and reliability. Learners should prioritize programs that include real scenarios and operational troubleshooting.
7) aiopsschool
aiopsschool may be a good fit for professionals interested in observability, automation, and intelligent operations approaches. After building Kubernetes security knowledge through CKS, some learners want to expand into detection, monitoring intelligence, and automation-led response. In that case, an AIOps-oriented learning ecosystem can add value. It can help professionals think at scale when operating complex systems. For teams running cloud-native environments, combining security awareness with operational intelligence is increasingly useful. Practical labs and real monitoring workflows should be a key evaluation factor.
8) dataopsschool
dataopsschool can support data engineers and platform teams who run data pipelines and services in cloud-native environments. If data workloads are deployed on Kubernetes, CKS knowledge becomes highly relevant for access control, secret handling, and operational safety. A DataOps-focused training path can help learners connect platform security with data delivery and governance workflows. This is especially useful for organizations managing sensitive or business-critical data processing. Learners should compare training based on real pipeline examples and operational support. Data platform reliability improves when security practices are built in.
9) finopsschool
finopsschool is relevant for professionals focused on cloud cost optimization and financial governance. While CKS is not a FinOps certification, Kubernetes security understanding helps in governance discussions because weak controls often create cost waste and recovery overhead. A FinOps-focused ecosystem can help practitioners work better with platform and cloud teams on policy-based usage. This is useful in organizations running shared Kubernetes environments. Learners should evaluate whether the training connects cost decisions with engineering realities. Secure, governed operations often lead to better cost predictability.
FAQs
1) Is CKS difficult for a working engineer?
CKS can feel difficult because it is practical and security-focused. However, it becomes much more manageable when you already have Kubernetes basics and follow a hands-on practice routine instead of relying only on theory.
2) How much time should I keep for CKS preparation?
That depends on your starting point. Professionals already working with Kubernetes may prepare faster, while those newer to Kubernetes security may need a longer plan (for example, 30–60 days) with regular practice.
3) Do I need strong security knowledge before starting CKS?
Not necessarily. You do need a strong Kubernetes foundation, but security depth can be built during preparation if you practice consistently and learn the reason behind each control.
4) Is CKS useful only for Security Engineers?
No. It is highly useful for DevOps Engineers, SREs, Platform Engineers, Cloud Engineers, and even Software Engineers who deploy to Kubernetes. Security in Kubernetes is a shared responsibility.
5) What should I know before starting CKS?
You should be comfortable with Kubernetes basics (pods, deployments, services, namespaces), Linux command-line usage, and general container concepts. Basic networking knowledge is also helpful.
6) Should I do CKS before a broader DevOps program?
If your current work is Kubernetes-heavy, doing CKS first can be a smart move. If you need stronger cross-functional foundations in DevOps/DevSecOps/SRE, you may choose a broader program like MDE before or after CKS.
7) How valuable is CKS for career growth?
CKS is valuable because Kubernetes security skills are directly useful in production environments. It can strengthen your profile for DevSecOps, SRE, platform engineering, and cloud security roles.
8) Does CKS help in real projects or only in interviews?
It helps in both, but the biggest value is in real projects. You can use CKS learning to improve hardening, access control, workload safety, and operational monitoring in your current environment.
9) Is CKS good for engineering managers?
Yes, especially for managers leading cloud-native teams. Even if they are not deeply hands-on, understanding CKS-level topics helps in hiring, planning, risk reviews, and technical decision-making.
10) Can a Software Engineer benefit from CKS?
Yes. Software engineers deploying applications to Kubernetes can improve their deployment security practices, secret usage, and collaboration with platform/security teams.
11) What is the best next certification after CKS for broader opportunities?
A strong cross-track next step is Master in DevOps Engineering (MDE) because it broadens your knowledge across DevOps, DevSecOps, and SRE. The MDE page explicitly positions the program around those combined principles.
12) What should I do immediately after completing CKS?
Use the knowledge at work. Build security checklists, review RBAC and namespace boundaries, improve image controls, and propose a practical Kubernetes security improvement roadmap for your team.
FAQs
1) What is the main focus of Certified Kubernetes Security Specialist?
The main focus is securing Kubernetes platforms and workloads through practical controls such as cluster hardening, access restriction, workload protection, supply chain security, and runtime monitoring.
2) Who gets the highest value from CKS?
Professionals working directly with Kubernetes in production—DevOps Engineers, SREs, Platform Engineers, Cloud Engineers, and Security Engineers—usually get the highest value.
3) Is CKS worth it if I already know Kubernetes well?
Yes. Kubernetes knowledge and Kubernetes security knowledge are not the same thing. CKS helps you move from operational familiarity to security-focused platform expertise.
4) Is CKS more practical or theoretical?
It is most valuable as a practical certification. You should treat it as a hands-on learning path and practice real tasks repeatedly.
5) What topics should I practice most during CKS preparation?
Spend extra time on RBAC, cluster hardening, system hardening, supply chain security, network policies, and runtime monitoring/logging because these areas are central to secure Kubernetes operations.
6) Can CKS support a DevSecOps career transition?
Yes. CKS is a strong bridge from DevOps to DevSecOps, especially for teams using Kubernetes as a core runtime platform.
7) What is the best cross-track path after CKS?
A strong option is Master in DevOps Engineering (MDE) because it expands your scope into DevOps, DevSecOps, and SRE practices.
8) How does CKS help organizations, not just individuals?
It helps organizations by building stronger Kubernetes security practices, improving platform standards, reducing avoidable security risk, and enabling better collaboration between platform, security, and application teams.
Conclusion
The Certified Kubernetes Security Specialist (CKS) is more than a certification for Kubernetes professionals—it is a practical skill-building path for secure cloud-native engineering. It helps you learn how to secure clusters, workloads, software supply chains, and runtime operations in ways that matter in real production environments. For engineers, it builds technical credibility and stronger project impact. For managers, it improves how teams plan, review, and govern Kubernetes platforms. If your organization uses Kubernetes seriously, CKS is a smart investment. Start with a realistic study plan, focus on hands-on practice, apply what you learn at work, and then expand into broader growth through paths like Master in DevOps Engineering (MDE) for long-term career progress.